Consumers spend nearly one million dollars online every sixty seconds, vulnerably entrusting their personal and financial info into the hands of business owners. While this is obviously great for the bottom line, attackers are becoming increasingly skilled at getting a hold of sensitive login and payment info such as credit card and bank account numbers. These annoying hackers don’t discriminate and will go anywhere regardless of the type of business or location. All they need is an untrusted router or IPS. This means that all public WiFi networks can be vulnerable to security threats. You need to know for certain that your website isn’t going to be one of them.
What is HTTP & HTTPS?
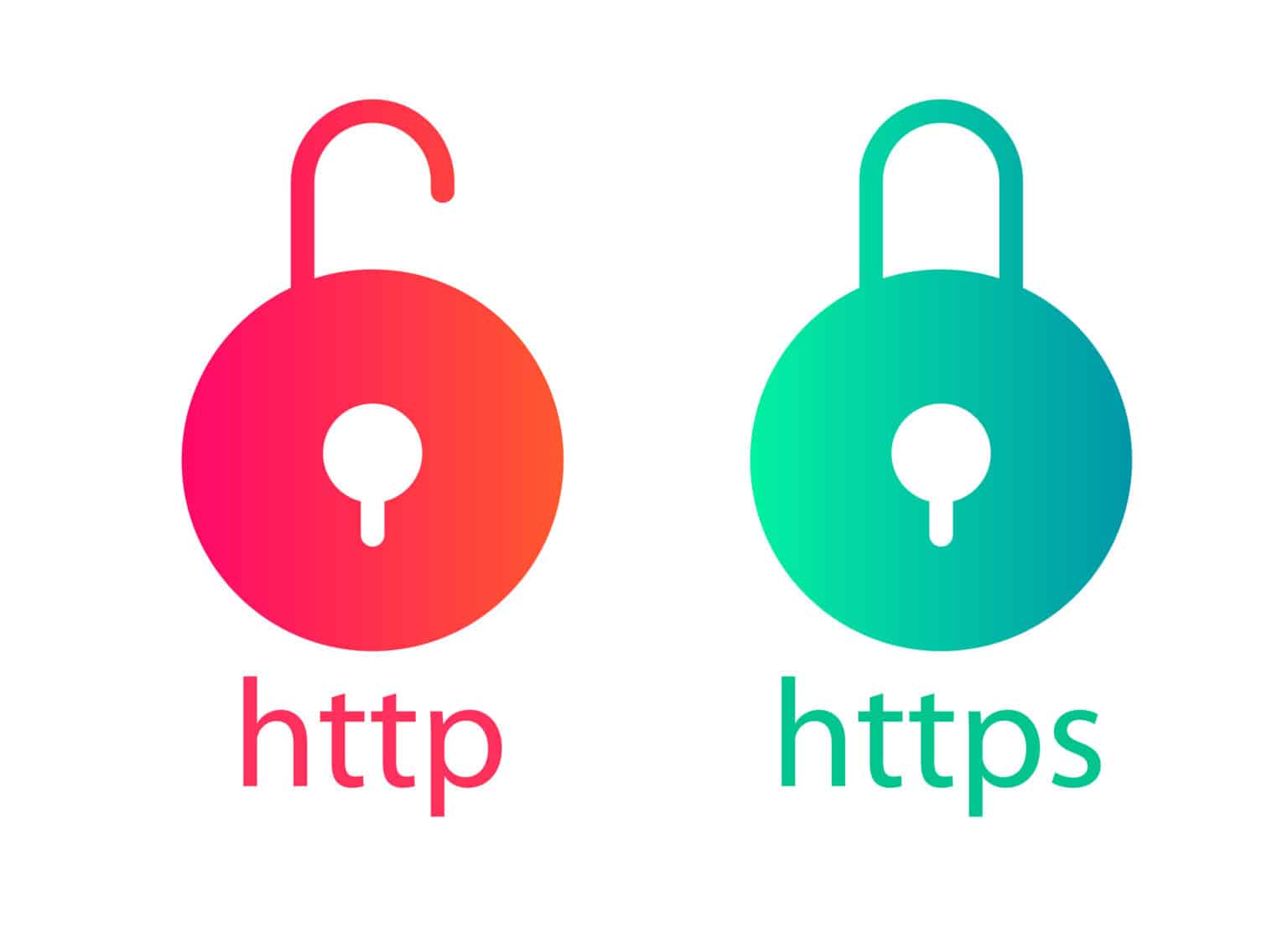
There are protocols for the transfer of sensitive info to the internet and this is where HTTPS and HTTP come into play:
HTTP stands for Hyper Text Transfer Protocol.
HTTPS stands for Hypertext Transfer Protocol Secure.
HTTPS encrypts HTTP requests and responses, ensuring that hackers do not see specific payment info. Instead, they see random, nonsensical characters. Basically, it’s like shipping off your household documents in a fireproof, indestructible lockbox with a secure combination. Only you and the recipient would know the combination. If the box were to fall into the wrong hands, your documents would be secure. The “wrong hands” wouldn’t have the combination.
What you should know is that multiple things occur during the formation of a HTTPS connection, but the most important thing to note is that HTTPS relies on Transfer Layer Security (TLS) encryption in order to secure connections.
Now, a lot of things happen when a HTTPS connection is formed. Mainly, HTTPS relies on TLS (Transfer Layer Security) encryption to secure the connections.
Let’s talk about TLS Certificates:
TLS (also known as SSL or SSL/TLS) certificates are a type of digital certificate issued by a Certificate Authority (CA). Installing a TLS certificate on your server is the only way to enable HTTPS protection on your company website.
The CA acts as a trusted third-party in the relationship between server and client. While TLS certificates can be issued by almost anyone, browsers only support publicly trusted CA’s. It’s easy to check website TLS certificates by clicking on the lock icon in the browser’s address bar. You will also be able to see the issuing CA and you can easily click through the certificate to review info such as the “issued to:” line. There are various types of validation protocol for TLS certs which determine whether the certificate will be free or paid.
- FREE TLS CERTS only do domain validation and they come with your hosting and CDN plan. A CDN is a network of servers linked together with the goal of delivering content as quickly, cheaply, reliably, and securely as possible.
While basic domain validation is great for websites and blogs that don’t utilize consumer personal and payment data, you’re going to need more than the basics for your business website.
- DV TLS CERTS give the appearance of security, but have no “Issued to:” line on their icon. “Let’s Encrypt”, a non-profit CA, issues the most common DV TLS cert which is used by most companies who offer automatically renewable, free TLS certs. DV-only certificates are the only TLS certificates issued at scale automatically.
- Organization Validation (OV) & Extended Validation (EV): It’s likely that your website collects sensitive payment info, so EV might be the better solution as its verification process is more rigorous. EV runs about the same price as OV and it is considered to be more trustworthy.
- Wildcard & SAN TLS certs are fabulous multitaskers as they secure numerous (sub)domains simultaneously and side step the need to purchase more than one TLS cert in order to perform multiple functions. EV TLS, for example, would be great for mcs.com, however an additional cert would be necessary for blog.mcs.com.
Wildcard certs also multitask in securing innumerable subdomains. SAN certs can also secure multiple domains.

HTTPS strengthens SEO
HTTPS beefs up your website’s privacy, security and SEO goals via:
- Verifying that the website is the correct one on the server.
- Mitigating third party tampering.
- Ensuring greater security for consumers.
- Communication/URL encryption.
- Personal data protection (browsing history, credit card info, etc.).
- Preservation of referral data.
- Lightweight ranking signal.
- Enhances security and site speed.
Furthermore, there is a strong theory which suggests that HTTPS has the potential to improve website dwell (a strong ranking factor). Also, bear in mind that if your company website is on HTTP and you are relying on Google Analytics, for example, for website analytics, referral data will NOT be passed from HTTPS to HTTP pages. Most of the web runs on HTTPS which is how most clicks on links from other websites (your referral traffic) is sourced.
HTTPS also utilizes modern protocols (such as TLS 1.3 and HTTP/2), enhancing your website’s overall speed and security. This might not make sense as HTTPS can appear slower than HTTP on paper due to the multiple added security layers, BUT it is a prerequisite for the utilization of modern security measures and up-to-the-minute performance technology. Staying current is crucial as Google views page speed as a lightweight ranking factor.
The Setup Process:
- Start with HTTPS at the onset. This will avoid migration errors and you won’t need to worry about HTTP. Your hosting provider or WordPress maintenance services Jacksonville can easily guide you through the necessary steps in support of the most current HTTP and TLS protocol version. The final step: implement HSTS.
- If your website is already HTTPS enabled, ask your hosting provider to guide you through the process of checking for common errors. You probably aren’t set up correctly.
- If your website is still running HTTP, the difficulty of migration will depend on some variables: website size/complexity, type of CMS, hosting provider and technical abilities.
While you might be capable of doing the migration yourself, here are some things you should take into consideration:
Review your CMS/server/hosting documentation and cautiously proceed. You’re going to need to take your time as there are multiple steps which must be executed on the migration checklist. This process could take a TON of time to complete and there’s no guarantee that you will be able to perform it correctly. Consult WordPress maintenance services Jacksonville in order to ensure a future-proof implementation and your sanity!
Sidestepping HTTPS migration mistakes:
Even if you could complete the entire HTTPS migration checklist, you’d probably still come across some errors. Here’s the deal:
In 2016, 10,000 top-ranking domains were found to have the following HTTPS mistakes:
- Sub-optimal HTTPS on 90.9% of domains.
- 65.39% of domains did not have HTTPS working as it should.
- Temporary 302 redirects on 23.01% of domains rather than permanent 301s.
It was pretty gruesome. You’d be wise to check for the most common migration mistakes:
- Are all of your website pages on HTTPS? Crawl your website thoroughly in order to find leftover HTTP pages (review your migration checklist). Ensure your crawler is up-to-date with all the required URL sources. You don’t want to leave any of those pages unchecked, however, be sure to note that pages which are not included in your sitemap which have zero links pointing to them won’t be discovered via crawling. Unfortunately, this happens with dedicated PPC landing pages quite frequently. You can export the URL list from FB Business Manager. Google Ads is another ad manager from which you could export a URL list. Next, ensure proper migration of orphaned pages and update to the newer HTTPS format in your campaign dashboard.
- Do you have HTTPS pages with HTTP content? A common mistake which occurs when the original HTML file uses HTTPS while loading BEFORE a resource file was updated to HTTPS. This particular issue is manifest in crawling and internal pages reports.
- Are your internal links updated to HTTPS? Unnecessary redirects occur when internal links to HTTPS are not updated, so be sure to update, update, update!
- Are your tags updated to HTTPS? Canonical and Open Graph tags and URLs need to be updated to HTTPS. Canonical tags inform Google regarding the most authoritative pages among a collection of duplicate (or similar) pages. Open Graph tags are used to optimize social media posts, some of which require URL tags. The easiest way to find pages with HTTP canonical and OG tags: set up a custom filter in Page Explorer and rewrite to https:// once migration is completed.
- Do you have failed redirects? A simple site audit will allow you to spot failed redirects. Just review the report and correct the issues. Upon clicking on “View affected URLs,” you’ll see a full report with default columns and metrics, allowing you to get a detailed breakdown of all the affected URLs.
Split up the redirects, but strive for the least number of redirects.
Review the number of inlinks (URLs that link to the URL affected by the redirect chain). Exchange the links on those pages for URLs that return a 200 HTTP status code and click through the number of inlinks to review all of them. Be sure to check the redirect chain URL inlinks as they will be tagged “standard 301 redirects” in the 3XX Redirects report when performing subsequent crawling.
In Closing:
Between 88-99% of Chrome browsing time is spent on HTTPS websites which means that the majority of high-traffic websites use HTTPS. While there is still much to be desired regarding TLS support quality, the migration process isn’t the “be all, end all” of HTTPS setup. Consumers will benefit from your efforts to “keep up with the Joneses” when it comes to trends in web performance and security. They will appreciate your implementation of up-to-the-minute features as manifest evidenced in your company’s bottom line.